A few years ago, the best way for a criminal to prepare for retirement was to rob a bank by physically breaking in or by attacking an armored truck. With the increase in physical security, criminals have adapted and found new ways to ‘cash-in’, without the need of guerrilla attacks.
In today’s world, bank heists are carried out via the Internet by cybercriminals and, directly attacking consumers using highly sophisticated weapons such as Banking Trojans engineered for one purpose: Stealing your online and e-banking credentials!
Banking Trojans are not new. The most notorious in the family is ZeuS (a.k.a ZBOT), first under the spotlight in 2007, when it was used by cybercriminals to steal credentials and information from the United States Department of Transportation. However, the DOT heist was not its’ biggest achievement and has since infected millions of machines, creating hundreds of millions of dollars in losses.
In 2011, ZeuS’ source code was publicly released by its creator. Since then, most of the new Banking Trojans discovered show traits and pieces of ZeuS. The most notable Banking Trojans discovered Post-ZeuS are: Gozi, Carberp, Spyeye, Dyre, and Dridex.
Gozi was also first discovered in 2007, but has been used in an attack as recent as yesterday (7th of April 2016)! 9 years after its discovery, the leading Swiss online news portal reported a successful attack resulting in Gozi’s injection on their news platform, affecting anyone who accesses the infected section. According to Swiss Governmental Computer Emergency Response Team, this is not an isolated incident. The Gozi campaign is targeting Swiss internet users since Spring of 2015!
HOW CAN YOU GET INFECTED?
There are two main ways to be infected with a Banking Trojan:
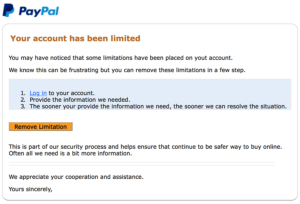 Phishing Scams via email are the number one infection vector. Most of them are caught by our spam filter, but in some cases, they arrive in our inbox with the same look & feel as emails we would receive from our bank, ISP, eBay, PayPal, etc.
Phishing Scams via email are the number one infection vector. Most of them are caught by our spam filter, but in some cases, they arrive in our inbox with the same look & feel as emails we would receive from our bank, ISP, eBay, PayPal, etc.
Drive-by-Downloads is the second vector. This term describes how a malware can infect your computer by visiting a website that was compromised. The Swiss online news platform mentioned previously is a very good example of a drive-by-download.
WHAT DO THEY DO?
Banking Trojans can be considered the Swiss Army Knife for cybercriminals, as it is loaded with several features to help them avoid detection and make sure any desired information can be stolen from our computer.
 |
 |
 |
 |
| Records what you type on your keyboard | Takes screenshots on a regular basis | Evades detection from your anti-virus using sophisticated techniques | Steals your usernames and passwords saved in your web browser |
 |
 |
 |
 |
| Downloads and Installs other malwares such as ransomwares | Creates mirrored versions of websites you surf on to steal your data | Attempts to infect your Phone to bypass two-factor authentication solutions | Collects sensitive info from your temporary files and web browser cache |
Banking Trojan can be a deceiving term. People may think they are not at risk if they do not use online banking, but they are wrong. Unfortunately, Banking Trojans are not only used to steal your banking & financial information, but any information that may have a financial value!
HOW CAN I PROTECT MYSELF?
Protecting yourself starts with a certain cyber hygiene. You periodically clean your house to remove dirt and kill bacteria, and the same concept is relevant (and needed) for your computer. You should update your operating system and all its running software such as Antivirus, PDF readers, Office Suite, Browsers and its components (Java, Flash, Silverlight, etc.) on a regular basis.
In addition, it is important to be careful which websites you visit. Be mindful that websites offering torrents, illegal video streaming, hacking, and porn content are the #1 websites serving malware.
In our current world, ‘zero risk’ no longer exists. Having an antivirus and an updated computer will not eliminate the Banking Trojan threat, but will reduce it. Due to an increase in e-banking usage, these types of malware continue to become more sophisticated, and keep rising from the dead even after FBI and other governmental agencies seizures. The problem must be tackled in a different way, which is why wizlynx has recently released a new service for consumers and enterprises that adds an additional layer of protection. NowProtected is a state of the art armored browser that identifies and prevents malicious code injection. Our solution protects you against Banking Trojans that may already reside on your computer by blocking its functionalities: Key loggers, Screen scrapers, Cache miners, and more.
Don’t wait to get hacked to react, get protected now!
Yann C.
Head of Cyber Security Services @ wizlynx group





