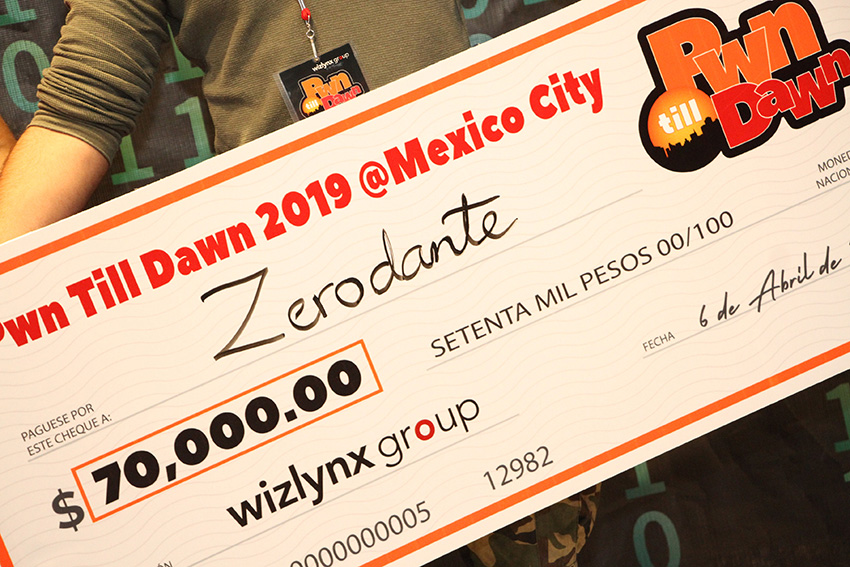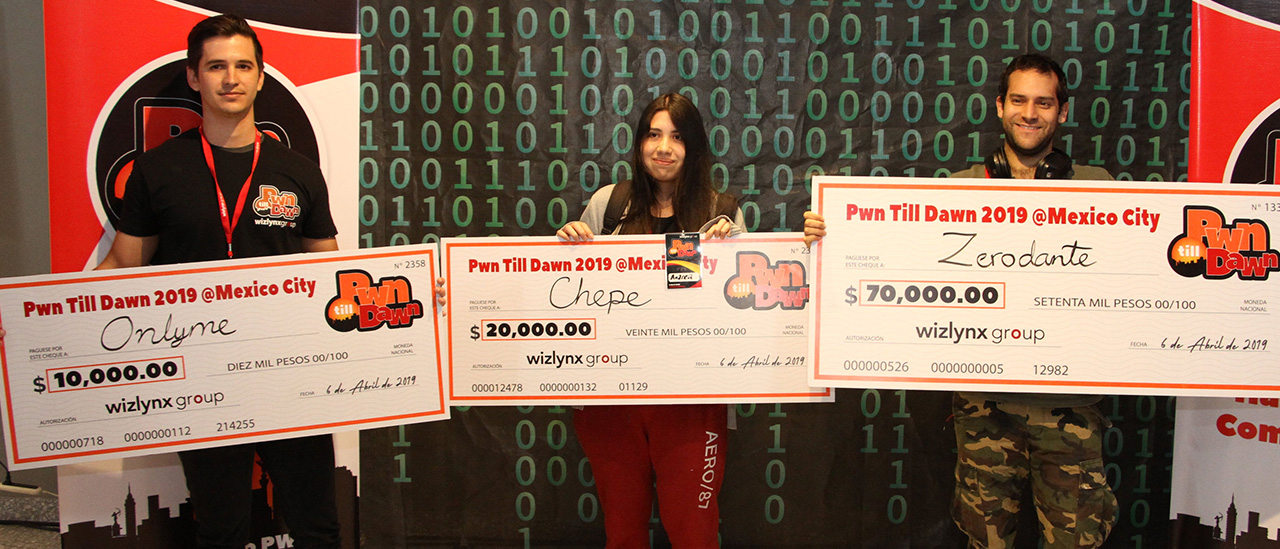

| 1st: | Zerodante | 735 |
| 2nd: | chepe | 700 |
| 3rd: | onlyme | 635 |
| 4th: | xxmeshx* | 635 |
| 5th: | EvilMachine | 610 |
| 6th: | servandomiguel | 540 |
| 7th: | Puerko | 535 |
| 8th: | mmmmm | 435 |
| 9th: | ss341 | 350 |
| 10th: | Sparta177iz | 310 |
| 11th: | VictorM | 275 |
| 12th: | chr0n1cle | 235 |
| 13th: | M23Gzz | 200 |
| 14th: | lalospidey | 185 |
| 15th: | Cabeza de Nabo | 175 |
| 16th: | Aa35go | 160 |
| 17th: | Cybernetic | 135 |
| 18th: | Chris | 125 |
| 19th: | ZeroLuis | 110 |
| 20th: | zilikos | 110 |
The competition started slowly on this past Saturday morning, with the participants performing the due reconnaissance of the vulnerable machines in the network, trying to find their first target. After a few minutes most of the contenders already found point-awarding flags. From the start of the contest, it was clear that most of the players were on the same level, even though the skillset of each one was different. We saw participants trying to brute force the systems and others trying to break into our systems with more gentle techniques.
While machines were very hard to penetrate, most participants did not give up and tried harder, knowing that adversity would strengthen their techniques, as well as assist in gaining new skills.
After the first half of the competition, the top positions were occupied by three participants that were surpassing each other every few minutes.
...
Read More