According to Wikipedia “Ransom is the practice of holding a prisoner or item to extort money or property to secure their release, or it may refer to the sum of money involved”. Do you want to understand what a ransomware does? Well, take the definition above and apply it to files and data.
 This will give you an idea of the modus operandi of this class of malware. However, your data and files are not really kidnapped. They are still there on your computer, but now they are encrypted, and your operating system is not able to read them anymore. Does this mean your data is lost forever? Well no…because this would not give the attacker any chance to obtain a reward.
This will give you an idea of the modus operandi of this class of malware. However, your data and files are not really kidnapped. They are still there on your computer, but now they are encrypted, and your operating system is not able to read them anymore. Does this mean your data is lost forever? Well no…because this would not give the attacker any chance to obtain a reward.
Your files can be decrypted using a private key that the malicious entity would sell to you for hundreds of dollars. This key is able to decrypt all your files and get the situation back to normal.
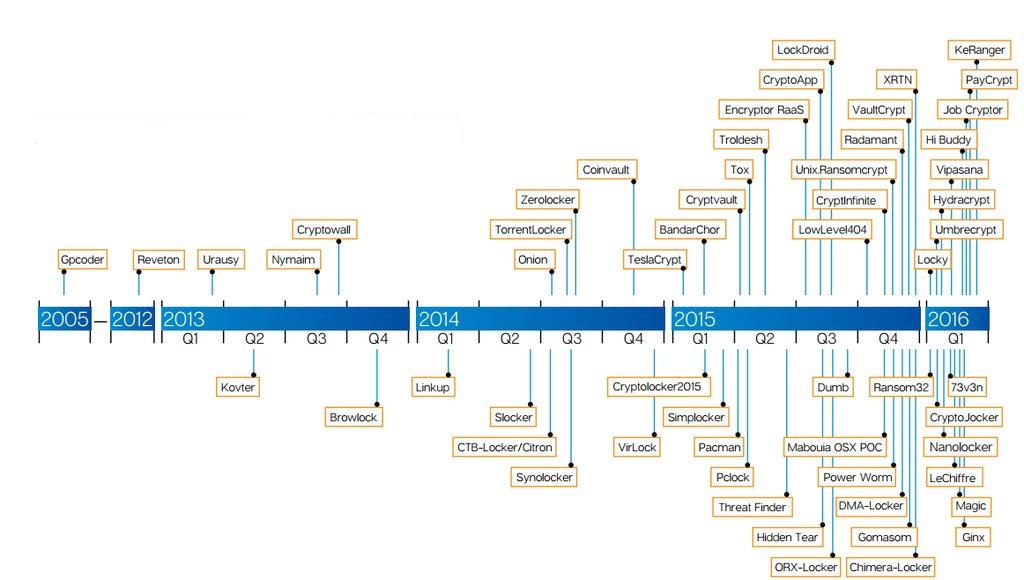
Ransomware has existed since 2005, but only has had consistent growth since 2015, tripling in numbers of existence!
HOW CAN YOU GET INFECTED?
The channels that this type of malware uses to spread are pretty much the same as any other common malware like Trojan Horses such as drive-by-downloads, stealth downloads, malvertising and/or distribution via email.
The most commonly used technique to reach user machines is, as usual, phishing: tricking a user to click on a malicious link seems still the cheapest and most efficient way to spread any infection.
However, a new kind of ransomware recently appeared on the net. It is able to spread itself without any human assistance, just like a worm does, taking advantage of application server vulnerabilities.
HOW CAN YOU PROTECT YOURSELF??
Beside the defense that should be in place for every type of malware (such as an regularly applied software, OS and anti-virus updates and not to forget constant end-user training), we think particular attention has to be put on regular data backup. Consistently keeping a recent backup stored on a different machine could make the ransomware action harmless, as long as the backup copy of the data is still accessible to you and the integrity is intact. This, combined with a decent active defense and the right common sense (do not click on suspect links, download files only from trustful sources and be careful in which site you are visiting), can guard you against ransomware.
SHOULD YOU PAY??
Things happen. Maybe you did not pay attention, clicked on a link and got infected. What is the best thing to do? Should you pay? Unfortunately there is no universal answer to this question. The first step to take is to verify if a decryption tool exists for the ransomware that has infected your system. If not, there are two aspects to consider:
- Price of ransoms usually range between 100$ – 600$. Is your data worth that amount? If your latest backup is outdated, generally the answer is yes.
- Paying the ransom is as good as supporting a criminal organization. Often, law enforcement suggests not paying in order to discourage extortion. However, this is easier said than done when it is not your data that’s on the line!
Pay attention, rather than pay for your data!
Christian F.
Senior Security Analyst @ wizlynx group
Ransom definition: https://en.wikipedia.org/wiki/Ransom





